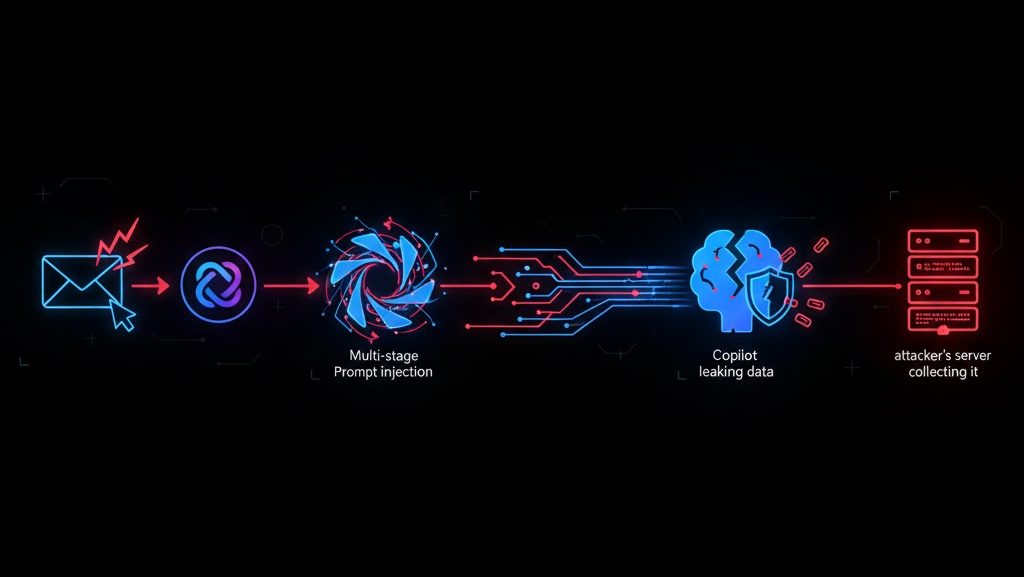
Claude Code Security: Architecture & Limitations
Scanning Flow Overview 1. Repository InputConnect or upload codebase → 2. Semantic AnalysisMap data flows & interactions → 3. Vulnerability DetectionIdentify logic & access issues → 4. Severity [...]